Blog
Risk Assessment in Data Migration Projects
A Complete Guide to Secure & Successful Migration
Why Risk Assessment is Crucial in Data Migration
Data migration involves transferring large volumes of sensitive information across systems, platforms, or environments. Risks can arise from:
Data corruption
Security vulnerabilities
System incompatibility
Human errors
Regulatory non-compliance
A structured risk assessment ensures that potential issues are identified and mitigated before migration begins.
What is Risk Assessment in Data Migration?
Risk assessment is a systematic process of identifying, analyzing, and prioritizing risks that may impact the migration project’s success.
It helps organizations:
Protect data integrity
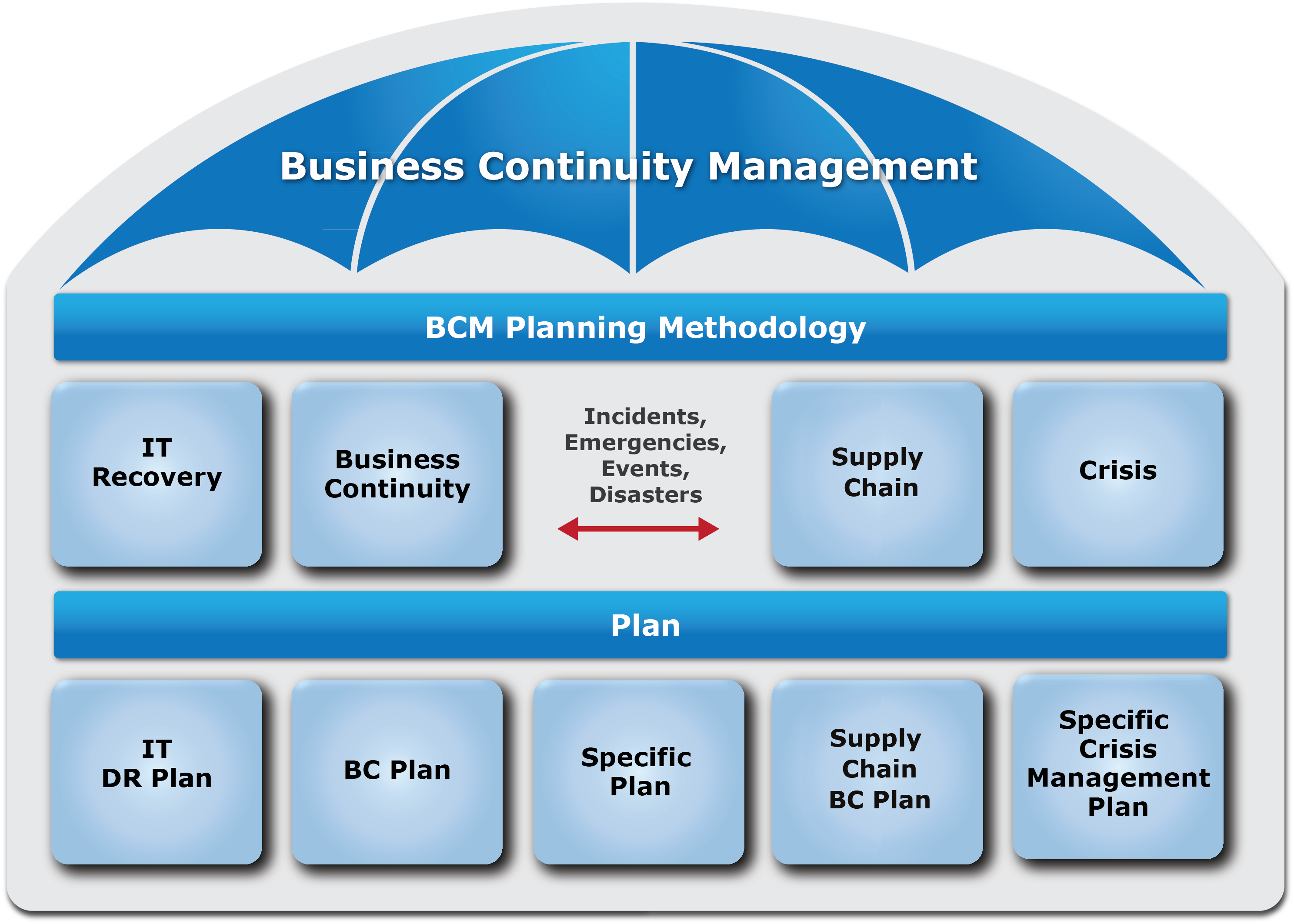
Maintain business continuity
Ensure regulatory compliance
Avoid financial losses
Reduce operational disruptions
Key Risks in Data Migration Projects
1️⃣ Data Loss or Corruption

Improper mapping, transformation errors, or interrupted transfers can corrupt or lose data.
Mitigation:
Perform full backups
Validate data before and after migration
Use checksum verification
2️⃣ Security & Cybersecurity Risks
Data in transit is vulnerable to breaches, ransomware, and unauthorized access.
Compliance with regulations such as:
General Data Protection Regulation
Health Insurance Portability and Accountability Act
Payment Card Industry Data Security Standard
requires strong encryption and access controls.
Mitigation:
Encrypt data in transit and at rest
Implement role-based access control (RBAC)
Use secure transfer protocols
Monitor logs in real time
3️⃣ Downtime & Business Disruption
Migration failures can cause prolonged downtime, impacting revenue and customer trust.
Mitigation:
Plan phased migration
Schedule off-peak transitions
Implement rollback strategies
Test in staging environments
4️⃣ Compatibility & Integration Issues
Legacy systems may not align with modern cloud or ERP platforms.
Mitigation:
Conduct system compatibility analysis
Perform pilot migrations
Validate schema mapping
5️⃣ Regulatory & Compliance Risks
Improper handling of sensitive data can lead to heavy fines and legal consequences.
For example, GDPR penalties can reach up to 4% of annual global turnover.
Mitigation:
Conduct Data Protection Impact Assessment (DPIA)
Maintain audit trails
Document lawful processing basis
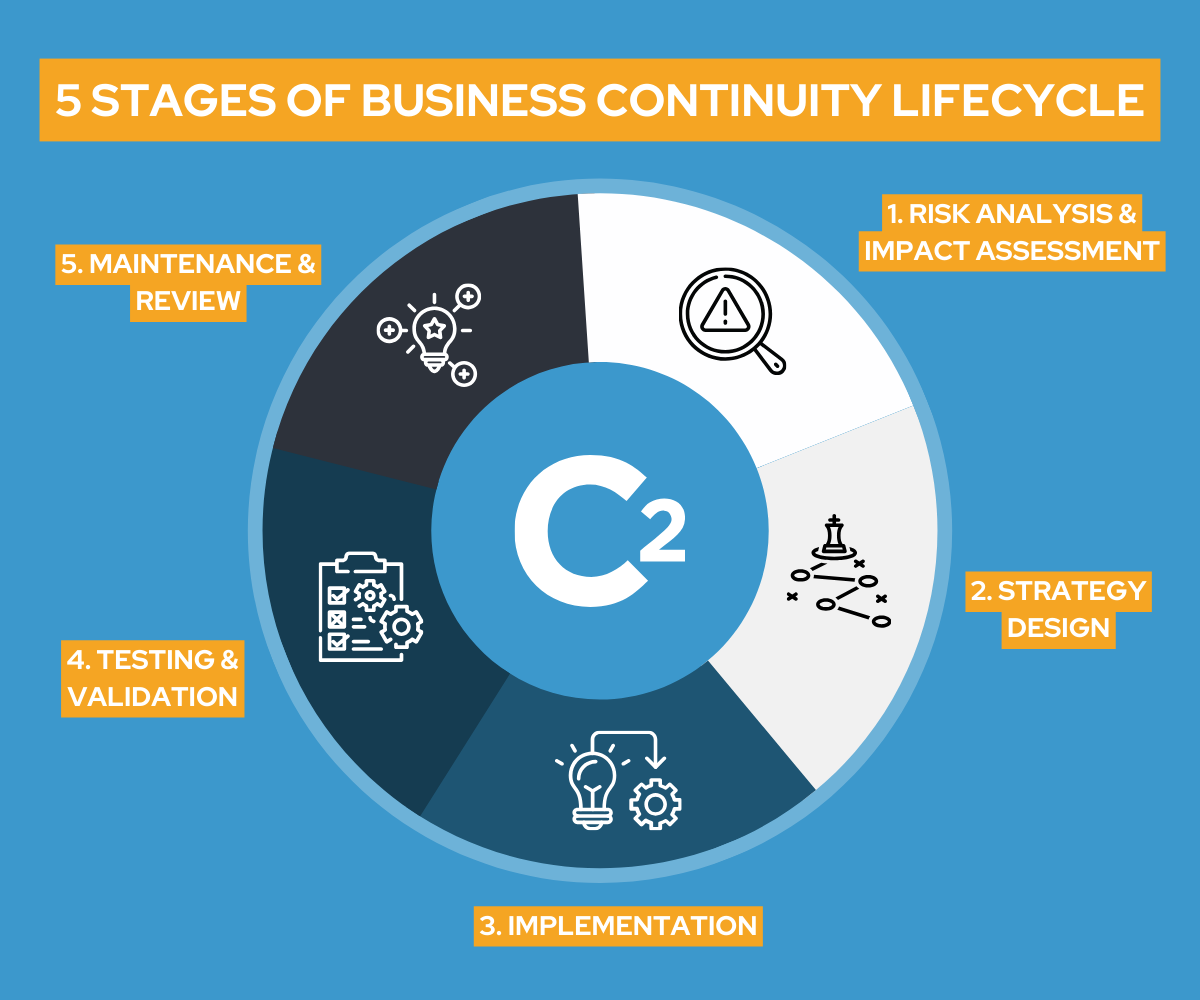
Step-by-Step Risk Assessment Framework
✅ Step 1: Identify Assets
List:
Databases
Applications
Sensitive data categories
Infrastructure components
✅ Step 2: Identify Threats
Common threats include:
Human error
Malware attacks
Insider threats
System failure
Network interruptions
✅ Step 3: Evaluate Vulnerabilities
Assess:
Outdated software
Weak encryption
Poor access management
Lack of monitoring
✅ Step 4: Analyze Impact & Probability
Use a risk matrix to classify risks as:
Low
Medium
High
Critical
✅ Step 5: Develop Mitigation Strategies
Implement preventive and corrective controls.
Risk Matrix Example for Data Migration
| Risk | Probability | Impact | Risk Level |
|---|---|---|---|
| Data loss | Medium | High | High |
| Security breach | Low | Critical | High |
| Downtime | Medium | Medium | Medium |
| Mapping errors | High | Medium | High |
Best Practices for Minimizing Migration Risks
🔹 Conduct Pre-Migration Data Audit
Understand what data is being moved.
🔹 Clean & Standardize Data
Remove duplicates and obsolete records.
🔹 Use Automated Migration Tools
Reduces human error.
🔹 Implement Backup & Recovery Plan
Ensure quick restoration if failure occurs.
🔹 Perform Multiple Testing Cycles
Unit testing
Integration testing
User Acceptance Testing (UAT)
🔹 Monitor Post-Migration Performance
Track system stability and data accuracy.
Role of Encryption & Secure Architecture
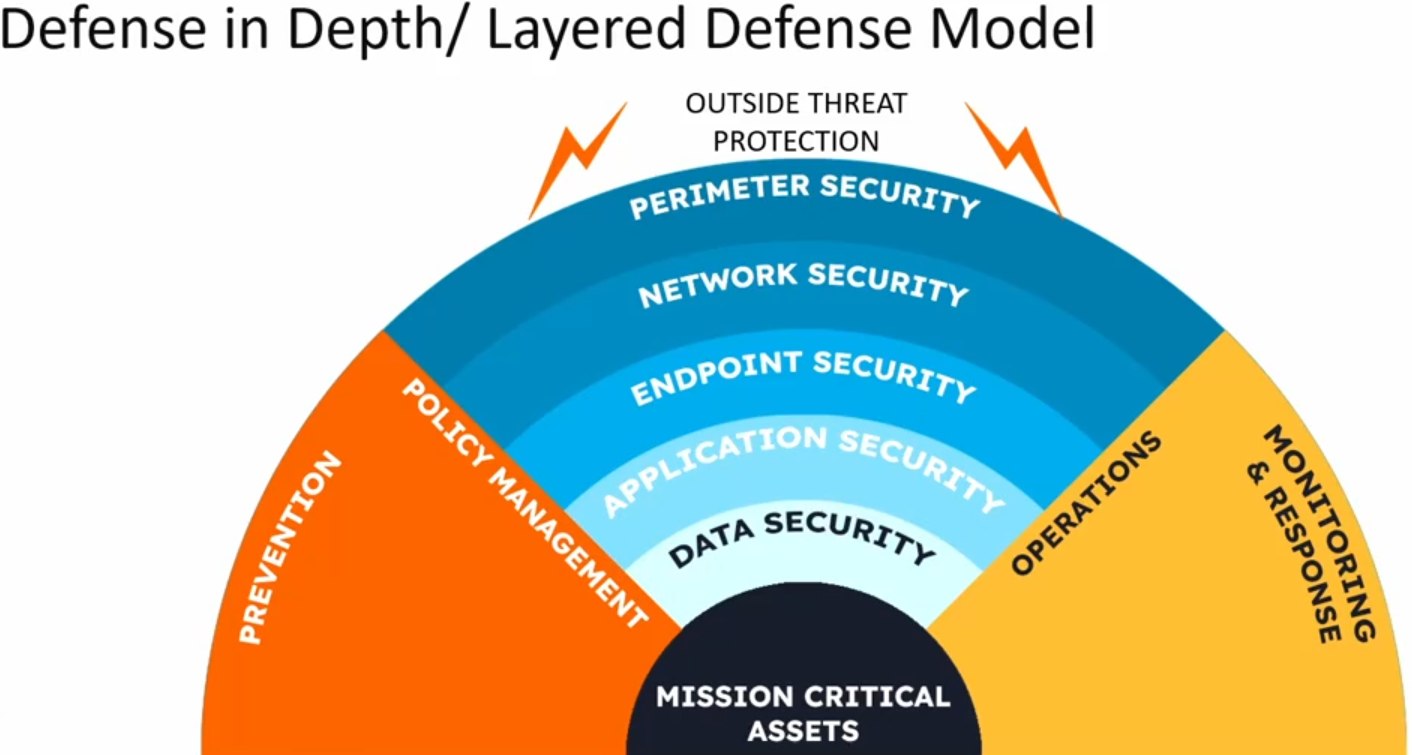
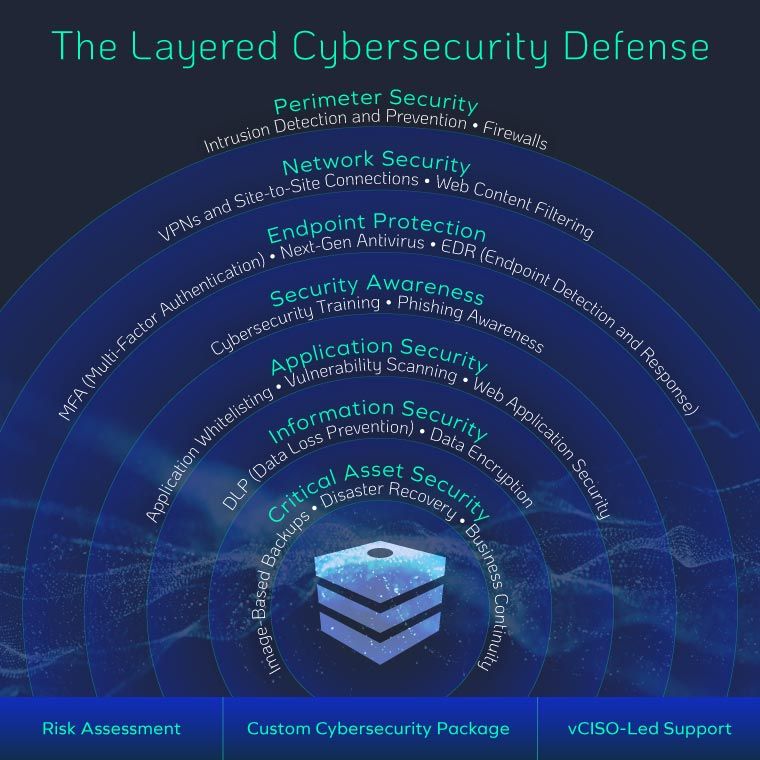
Secure architecture reduces risk exposure by:
Encrypting data at rest and in transit
Implementing multi-factor authentication (MFA)
Restricting administrative privileges
Enabling continuous monitoring
Security must be integrated from planning to post-migration validation.
Common Mistakes in Risk Assessment
❌ Skipping detailed data mapping
❌ Ignoring regulatory requirements
❌ Underestimating downtime impact
❌ Lack of stakeholder communication
❌ No rollback strategy
Proactive planning prevents reactive crisis management.
Benefits of Proper Risk Assessment
✔ Higher migration success rate
✔ Reduced downtime
✔ Improved data integrity
✔ Enhanced security posture
✔ Regulatory compliance
✔ Increased stakeholder confidence
Risk assessment transforms migration from a risky operation into a controlled transition.
Industries Where Risk Assessment is Critical
Healthcare
Banking & Finance
E-commerce
Government
SaaS platforms
Manufacturing
Any organization handling sensitive data must prioritize structured risk evaluation.
Conclusion
Risk assessment in data migration projects is not optional — it is essential for ensuring data security, compliance, and operational continuity. By identifying threats, evaluating vulnerabilities, and implementing mitigation strategies, businesses can reduce failures and achieve seamless migration outcomes.
A proactive risk management approach ensures that digital transformation initiatives remain secure, compliant, and successful.