Blog
Secure Data Transfer Protocols
A Complete Guide to Safe & Encrypted Data Transmission
In today’s digital ecosystem, organizations continuously transfer sensitive data between systems, cloud platforms, third-party vendors, and remote teams. Without secure data transfer protocols, this information becomes vulnerable to cyberattacks, data breaches, and compliance violations.
This comprehensive SEO-optimized guide explains the most secure data transfer protocols, how they work, and how to choose the right one for your business.
Why Secure Data Transfer Protocols Matter
When data moves across networks, it can be intercepted through:
Man-in-the-middle (MITM) attacks
Packet sniffing
DNS spoofing
Unsecured public Wi-Fi
Using encrypted protocols ensures:
🔐 Confidentiality
🛡 Data integrity
👤 Authentication
📜 Regulatory compliance
Secure transfer protocols are essential for industries like banking, healthcare, SaaS, and government.
What Are Secure Data Transfer Protocols?
Secure data transfer protocols are communication standards that use encryption and authentication mechanisms to protect data while in transit.
They prevent unauthorized access, tampering, and data leaks during transmission over public or private networks.
Most Common Secure Data Transfer Protocols
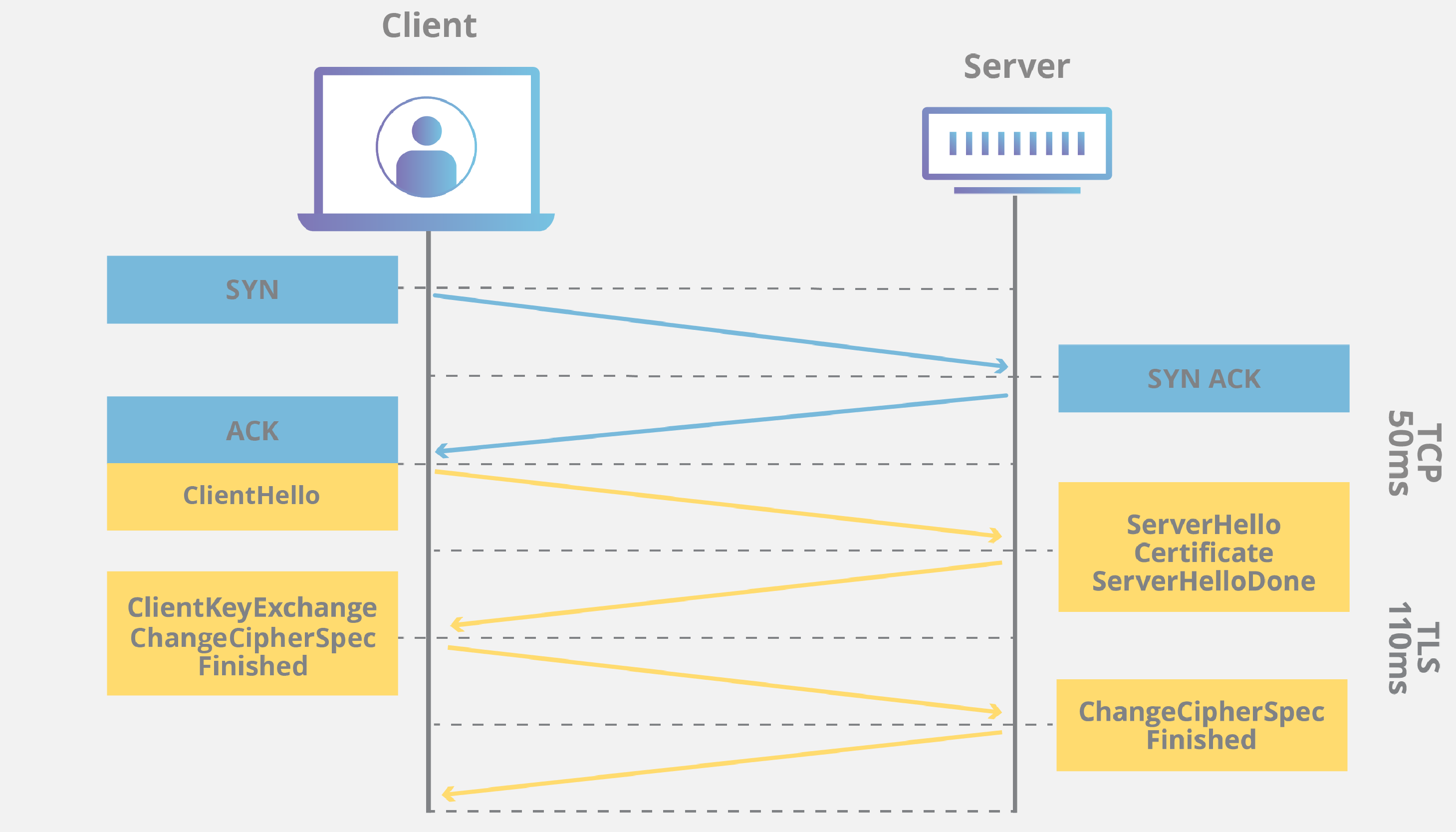
1️⃣ HTTPS (HyperText Transfer Protocol Secure)
4
HTTPS is the secure version of HTTP. It uses SSL/TLS encryption to secure web traffic.
Built On:
SSL (Secure Sockets Layer)
Transport Layer Security
Best For:
Websites
Web applications
APIs
E-commerce platforms
Benefits:
✔ Encrypts browser-to-server communication
✔ Ensures certificate-based authentication
✔ Protects login credentials and payment data
2️⃣ SFTP (Secure File Transfer Protocol)
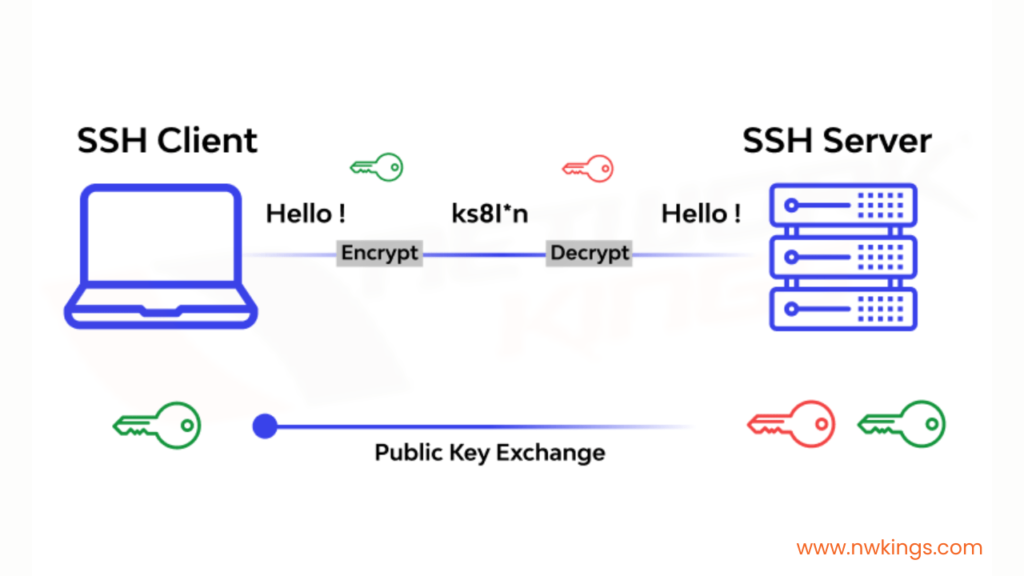
SFTP operates over SSH (Secure Shell) and encrypts both commands and data.
Built On:
Secure Shell
Best For:
Secure file sharing
Enterprise data exchange
Server backups
Database exports
Benefits:
✔ Strong encryption
✔ Authentication via SSH keys
✔ Firewall-friendly
3️⃣ FTPS (File Transfer Protocol Secure)
FTPS adds SSL/TLS encryption to traditional FTP.
Best For:
Businesses upgrading from legacy FTP
Secure file transfer over SSL
Note:
Less firewall-friendly than SFTP due to multiple ports.
4️⃣ SCP (Secure Copy Protocol)
SCP also runs over SSH and allows secure file transfers between hosts.
Best For:
Quick server-to-server file transfers
IT infrastructure operations
5️⃣ VPN (Virtual Private Network)
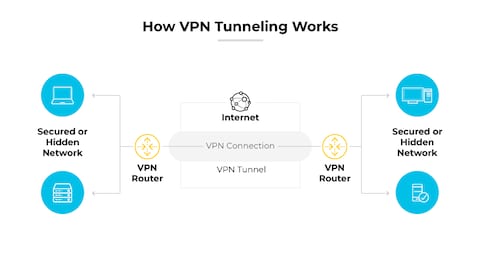
A VPN creates an encrypted tunnel between devices and networks.
Best For:
Remote employees
Cross-border data transfers
Secure internal communications
VPNs encrypt all traffic, not just specific files.
6️⃣ AS2 (Applicability Statement 2)
AS2 is widely used in EDI (Electronic Data Interchange).
Best For:
B2B data exchange
Supply chain communications
Industries like retail and logistics rely heavily on AS2.
Comparison of Secure Data Transfer Protocols
| Protocol | Encryption | Best Use Case | Security Level |
|---|---|---|---|
| HTTPS | SSL/TLS | Web & APIs | High |
| SFTP | SSH | File transfer | Very High |
| FTPS | SSL/TLS | FTP upgrade | High |
| SCP | SSH | Server copy | Very High |
| VPN | Encrypted tunnel | Remote access | High |
| AS2 | SSL/TLS | B2B exchange | High |
Key Features of Secure Transfer Protocols
🔐 Encryption
Prevents unauthorized reading of data.
👤 Authentication
Verifies sender and receiver identities.
🔎 Integrity Checks
Ensures data isn’t altered during transmission.
🛡 Firewall Compatibility
Allows secure operation within enterprise networks.
Best Practices for Secure Data Transfer
✅ Use Strong Encryption Standards
Always use TLS 1.2 or higher.
✅ Implement Multi-Factor Authentication (MFA)
Adds an extra security layer.
✅ Disable Legacy Protocols
Avoid:
Plain FTP
HTTP
Telnet
✅ Use SSH Keys Instead of Passwords
Prevents brute-force attacks.
✅ Regularly Update Certificates
Expired SSL certificates can cause vulnerabilities.
✅ Monitor Transfer Logs
Track unusual activity in real-time.
Compliance & Regulatory Considerations
Secure transfer protocols help organizations comply with:
General Data Protection Regulation
Health Insurance Portability and Accountability Act
Payment Card Industry Data Security Standard
ISO/IEC 27001
Using encrypted protocols reduces legal risk and ensures secure cross-border data transmission.
Common Mistakes to Avoid
❌ Using outdated SSL versions
❌ Hardcoding credentials
❌ Sharing SSH keys insecurely
❌ Ignoring certificate expiry
❌ Using public Wi-Fi without VPN
Security is only as strong as its weakest link.
Secure Data Transfer in Cloud Environments
When transferring data to cloud platforms:
Enable TLS for all endpoints
Use secure APIs
Configure role-based access control (RBAC)
Encrypt backups
Audit cloud logs
Most major cloud providers support end-to-end encryption by default—but configuration is essential.
Future of Secure Data Transfer
Emerging technologies include:
Zero Trust Architecture
Quantum-resistant encryption
Blockchain-based file verification
AI-driven anomaly detection
As cyber threats evolve, secure transfer protocols will continue to advance.
Conclusion
Secure data transfer protocols are fundamental for protecting sensitive information in today’s connected world. Whether you're handling web traffic, enterprise file transfers, remote access, or B2B exchanges, choosing the right encrypted protocol is critical.
By implementing HTTPS, SFTP, VPNs, and strong encryption standards, businesses can ensure data confidentiality, integrity, and compliance.
Investing in secure data transmission is not optional — it’s a strategic cybersecurity necessity.